How do spam and phishing relate to one another in today’s ever-evolving threat landscape? Although both terms are often used interchangeably, they represent distinct yet interconnected cyberthreats. Spam and phishing emails are sometimes difficult to tell apart due to their similarities. Here’s a clear picture of the similarities they share: …
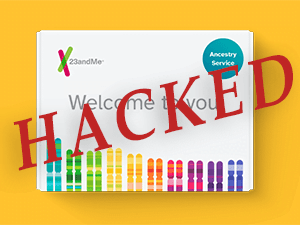
23 And You – The 23andMe Hack
A credential stuffing attack brought the popular genetic research company 23andMe to a crisis point last week, and its attacker is now offering to sell the names, locations, and ethnicities of millions of users. Credential stuffing is what happens when subscribers repeat the same username-password combinations on multiple websites, and …
Security-Savvy Employees Are Critical For Cyber Resilience
In chess, two rows of pieces are placed on either side of the board. These rows consist of eight pawns as the first line of defense against the enemy. The rest of the pieces behind them can move about effectively, depending on how you direct your pawns. But what if …
Phishing Awareness Tips To Help Stop Cyberattacks
Coming into contact with phishing scams has become a common occurrence for businesses. The combination of low upfront costs and a high success rate keeps phishing popular. Bad actors rely on phishing as a precursor to many dangerous attacks, such as ransomware, account takeover and business email compromise (BEC). In …
What Is The Dark Web?
The internet puts a galaxy of information at our fingertips and is an indispensable part of our professional and personal lives. But while all that information and utility has made our lives easier, it has also attracted the attention of criminal minds. The most mysterious section of the internet is …
Six Preventive Measures To Thwart Email-based Cyberattacks
Did you know that 9 in 10 cyberattacks start with a phishing email? Email is the most likely vector for employees to come into contact with a cyber threat, and every business is inundated with email daily. It’s critical that businesses do everything that they can to reduce their risk …
4 Dark Web Threats Businesses Need to Watch
The dark web is constantly evolving to present a thorny ticket of hazards for businesses. The point of origin for many of today’s most nasty and damaging cyberattacks, the dark web is the world’s third-largest economy and unlike many of the world’s industries, constantly growing. Dark web threats Cybersecurity Ventures …
GPT-3 Makes Phishing Scams Like These Worse
Phishing attacks have reached a new high, with cybercriminals favoring various phishing techniques to trap their victims in nasty phishing scams. Hackers use different phishing techniques as a precursor to many devastating cyberattacks like ransomware, business email compromise (BEC), malware and account takeover. As perpetrators use deceiving social engineering lures, …
What Are The Dangers of Business Email Compromise?
What’s the most expensive cyberattack that businesses face today? If you said business email compromise (BEC) you’re right. The FBI IC3 2021 Internet Crime Report showed that BEC packed a powerful punch against U.S. businesses that year. BEC complainants to IC3 suffered $2,395,953,296 in losses in 2021, 28% higher than …
New Wave of Supply Chain Cyber Attacks Expected
Throughout April, Shanghai and other major cities in China have been on lockdown due to recent COVID-19 outbreaks. Along with the ongoing war in Ukraine, these lockdowns have drastically impacted supply chains for industries around the world. We expect to see another wave of supply chain-related phishing and social engineering …