Understanding the Dark Web The dark web represents a hidden layer of the internet, accessible only through specialized browsers and encryption tools like Tor (The Onion Router) or I2P (Invisible Internet Project). Understanding the dark web isn’t just about technical curiosity – it’s about recognizing a significant source of cyber …
Cybersecurity Predictions for 2025: Challenges and Opportunities
The year 2024 was a whirlwind year for cybersecurity. From the fallout of high-profile ransomware attacks to the increasing commoditization of AI tools, the challenges kept mounting. Critical infrastructure vulnerabilities became starkly apparent, and identity theft reached unprecedented levels. Yet, amidst the chaos, we saw strides in defensive technologies, international …
Avoid Gift Card Draining Scams This Holiday Season
Gift cards make for easy, versatile gifts, especially during the busy holiday season. But they’re also prime targets for scammers who use “gift card draining” to steal funds before the recipient can even use the card. Let’s break down how these scams work and how you can stay safe. What …
Attackers Abuse DocuSign to Send Phony Invoices
Threat actors are abusing DocuSign’s API to send phony invoices that appear “strikingly authentic,” according to researchers at Wallarm. “Unlike traditional phishing scams that rely on deceptively crafted emails and malicious links, these incidents use genuine DocuSign accounts and templates to impersonate reputable companies, catching users and security tools off …
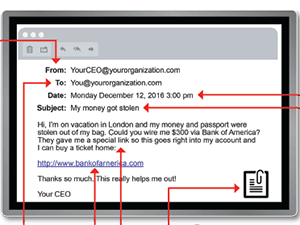
How To Recognize The Phishing Clues
In recognition of Cybersecurity Awareness Month, we wanted to share this guide for spotting a phishing email. The best way to avoid falling for phishing emails and clicking where you shouldn’t is to recognize the red flags. We recommend printing this guide and keeping it handy so you can spot …
Quick Take On Keeping Your Mobile Devices Secure
As remote work and connecting while traveling has become the norm, mobile device security responsibilities have also increased. We take our smartphones, tablets and laptops to airports, cafes and other public places, so the threat of a cyber attack targeting our devices is constant. There are some best practices to …
Half of Employees Fear Reporting Cybersecurity Mistakes
In the fast-paced world of business, mistakes are inevitable. Yet, when cybersecurity errors occur, many employees hesitate to report them. An estimated 50% of employees are afraid to report their cybersecurity errors because they dread the repercussions according to a report by ThinkCyber. This reluctance can seriously affect organizations, potentially …
8 Ways Cybercriminals Benefit from Stolen Data
Cybercriminals constantly seek to exploit stolen data for nefarious purposes. Understanding how they benefit from this data is essential for recognizing the risks and reinforcing security measures. According to the Identity Theft Resource Center’s (ITRC) 2023 Data Breach Report, the past year brought about a somber realization that cybercriminals have …
ATTENTION: Cyber Warning For Our Clients
We wanted to alert you to a cybersecurity threat our engineers have successfully mitigated for several of our clients recently. We’ve seen a rise in a specific type of cyber risk: malicious email links and attachments that appear to come from coworkers and other trusted sources like regular vendors or …
Why is Phishing Resistance Training So Essential?
Phishing is the gateway to many damaging cyber threats like business email compromise (BEC), ransomware and account takeover (ATO). Unfortunately, employees are inundated by phishing messages every day. They’re getting harder for users to spot thanks to technologies like generative artificial intelligence (AI). These are just a few of the …
- Page 1 of 2
- 1
- 2