Customer Relationship Management (CRM) software allows marketing teams to manage customer interactions better, track customer relationships, and monitor customer activity. It also will enable businesses to collect detailed profiles of their customers, allowing companies to target future products and offers to specific users. As technology becomes more sophisticated and affordable, …
SiriusXM Flaw Unlocks Vehicles and More
A somewhat concerning flaw has been fixed by SiriusXM that would allow unauthorized individuals to unlock doors remotely and start engines by only having the vehicle identification number (VIN). Sam Curry, a researcher at Yuga Labs, published a Twitter thread explaining the details of the discovered security flaw. The security …
End-to-End Encryption for Dropbox Business Users
Dropbox has announced its plans to purchase several key assets from Boxcryptor so that it is able to provide end-to-end encryption for its business users. In addition, the partial merger between the two companies will enable Dropbox to better meet its client’s needs, including an enhanced level of security for …
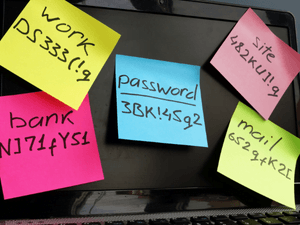
Lastest LastPass Security Incident
According to LastPass CEO Karim Toubba, the password manager has been hacked once again. A data breach occurred in the development environment only a few months ago, prompting LastPass to announce they had experienced a security breach on August 25, 2022. LastPass disclosed to its customers that a developer account …
Amazon Security Lake Aims to Enhance Cybersecurity for Businesses
The new security-focused data lake solution from Amazon Web Services (AWS), unveiled at re:Invent 2022, aims to give consumers more value from their security data. The Amazon Security Lake service aims to consolidate an organization’s security data from various on-premises and cloud-based sources into a single location to pinpoint security …
How AI is Transforming Businesses
While artificial intelligence (AI) is seen as a new phenomenon in mainstream society, it is not a new concept. As AI technologies increase, AI is becoming increasingly important for companies looking to stay competitive. What is AI Artificial intelligence is a broad term for any computer software that engages in …
Scammers Impersonating Refund Payment Portals
The FBI warns about scammers pretending to be refund payment gateways from financial institutions to steal sensitive information from unsuspecting victims. The federal law enforcement agency stated that scammers deceive victims into granting them access to their computers via email or phone calls by posing as representatives of technical or …
Twitter’s Data Leak Exposes Over 5.4 Million Users
Earlier this year, Twitter confirmed that an API vulnerability had caused a massive data leak containing non-public information for over 5.4 million Twitter users. Twitter denied claims that hackers had leaked the private information priorly. However, Pompompurin, the owner of the hacking forum Breached, stated they were responsible for exploiting …
Vice Society Claims Cincinnati State College Cyberattack
Data allegedly stolen from Cincinnati State Technical and Community College has been leaked after Vice Society attacked the campus. Many of the stolen documents were posted on the hackers’ websites. These documents date from several years ago until November 24, 2022, suggesting that threat actors still have access to the …
Malicious SEO Campaign Affects Thousands of Sites
In a massive malicious SEO campaign, cybercriminals are promoting low-quality Q&A sites by redirecting visitors to fake discussion forums. As a result, almost 15,000 sites have been compromised. In September 2022, researchers at Sucuri discovered the attacks. Each compromised site was found to contain approximately 20,000 files that were utilized …