How do spam and phishing relate to one another in today’s ever-evolving threat landscape? Although both terms are often used interchangeably, they represent distinct yet interconnected cyberthreats. Spam and phishing emails are sometimes difficult to tell apart due to their similarities. Here’s a clear picture of the similarities they share: …
Booking.com Multistep Phishing Campaign
One of the most common ways hackers manipulate online users is through malicious phishing campaigns. The popular travel reservation site Booking.com is the latest company at the center of a targeted cyberattack. Learn more about the dangerous ways hackers infiltrated the site and its impact on countless customers. How Phishing …
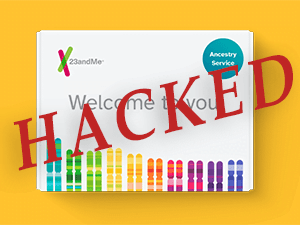
23 And You – The 23andMe Hack
A credential stuffing attack brought the popular genetic research company 23andMe to a crisis point last week, and its attacker is now offering to sell the names, locations, and ethnicities of millions of users. Credential stuffing is what happens when subscribers repeat the same username-password combinations on multiple websites, and …
Beware of This Microsoft Teams Phishing Campaign
Many people trust the contacts in their Microsoft Teams profiles and may immediately click any link they receive from what they think is a trusted contact. Hackers can exploit this trust by developing profiles almost identical to departments within their targets’ employment framework. Using these compromised accounts, hackers can send …
Ways To Protect Your Business and Make Social Media Safe for Your Company
Social media is used by everyone these days, even hackers. Hackers often try to steal your information from social media sites. Even though social media is a useful tool for businesses, it’s important to know what security risks it poses. We’ll show you how to keep your business safe and …
Businesses on Facebook Are Being Targeted by Password-Stealing Malware
With over two billion registered users, Facebook has become a target for advanced malware campaigns. These phishing campaigns steal unsuspecting users’ information. Businesses on Facebook are being targeted by password-stealing malware. What Is Malware? Malware is an insidious software that steals sensitive information from victims. The software exploits weak points …
Staying Safe from Phishing Scams
Hackers steal personal information from people who are vulnerable by making fake websites and sending phishing emails. If you fall for a phishing scam, private information like your credit card number could fall into the wrong hands. You can protect yourself from hackers in several ways, which is good news. …
How To Stay Safe and Secure From VPN Security Threats
Virtual private networks (VPNs) offer a safe path through the digital landscape. VPNs make a secure tunnel that encodes your information. This encryption protects details like what websites you visit or which apps you use. However, recent reports have shown that some VPNs need to be safer. Risks of Unsafe …
Discovering the Hidden Threat of Fileless Malware
What comes to mind when you hear the word malware? Most people may think of phishing messages containing malicious files. Once you download those files to your computer, they infect the entire system with a virus, making it impossible to use your computer. While this type of cyber-attack is dangerous, …
How To Stay Ahead of Cyber Attacks With Managed IT Services
With hackers and cyber threats on the rise, it’s all your business can do to stay safe in today’s digital climate. Managed IT services are integral for protecting businesses from cyber-attacks. Learn more about what these third-party cloud services do and how they can keep your business safe from outside …