How do spam and phishing relate to one another in today’s ever-evolving threat landscape? Although both terms are often used interchangeably, they represent distinct yet interconnected cyberthreats. Spam and phishing emails are sometimes difficult to tell apart due to their similarities. Here’s a clear picture of the similarities they share: …
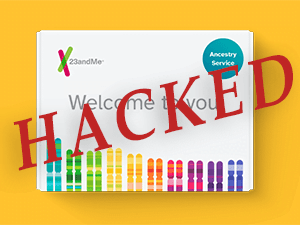
23 And You – The 23andMe Hack
A credential stuffing attack brought the popular genetic research company 23andMe to a crisis point last week, and its attacker is now offering to sell the names, locations, and ethnicities of millions of users. Credential stuffing is what happens when subscribers repeat the same username-password combinations on multiple websites, and …
How To Stay Ahead of Cyber Attacks With Managed IT Services
With hackers and cyber threats on the rise, it’s all your business can do to stay safe in today’s digital climate. Managed IT services are integral for protecting businesses from cyber-attacks. Learn more about what these third-party cloud services do and how they can keep your business safe from outside …
Security-Savvy Employees Are Critical For Cyber Resilience
In chess, two rows of pieces are placed on either side of the board. These rows consist of eight pawns as the first line of defense against the enemy. The rest of the pieces behind them can move about effectively, depending on how you direct your pawns. But what if …
How To Protect Yourself From the MOVEit Breach and Stay Safe Online
Hackers are always developing new ways to steal data from Internet users. The most recent data breach to impact millions involves MOVEit, a popular file transfer tool. Even though this breach exposes a lot of private information, there are ways to stay safe. This guide will show you how to …
Tech-Related Risks Businesses Need to Consider
As businesses use digital solutions, business owners and CEOs need to be aware of the possible risks of the tech they’ve chosen. Even though many solutions have good security features to protect their customers, you should still look at specific risks and how likely they will affect your business. Here …
How to Simplify and Strengthen Your Data Security
One of the biggest threats businesses face today is unauthorized data access. There are many ways for hackers to get in and steal valuable data. It’s your job to make it as hard for them as possible. Here are some strategies to make your data security more robust and straightforward. …
Phishing Awareness Tips To Help Stop Cyberattacks
Coming into contact with phishing scams has become a common occurrence for businesses. The combination of low upfront costs and a high success rate keeps phishing popular. Bad actors rely on phishing as a precursor to many dangerous attacks, such as ransomware, account takeover and business email compromise (BEC). In …
Scammers Use Government Websites to Advertise Hacking Services
Government websites are seen as sources people can trust. However, threat actors use this trust for their harmful purposes. Scammers recently used official websites to advertise their hacking services. This situation shows why businesses should be on the lookout and take more robust computer security measures to avoid being affected …
What Is The Dark Web?
The internet puts a galaxy of information at our fingertips and is an indispensable part of our professional and personal lives. But while all that information and utility has made our lives easier, it has also attracted the attention of criminal minds. The most mysterious section of the internet is …